
- /
- Notes/
Notes
I’m on a (very long) journey to digitize all my handwritten notes. This is an archive of those notes, for my personal use. This archive is not intended for commerical use.
Computer Vision
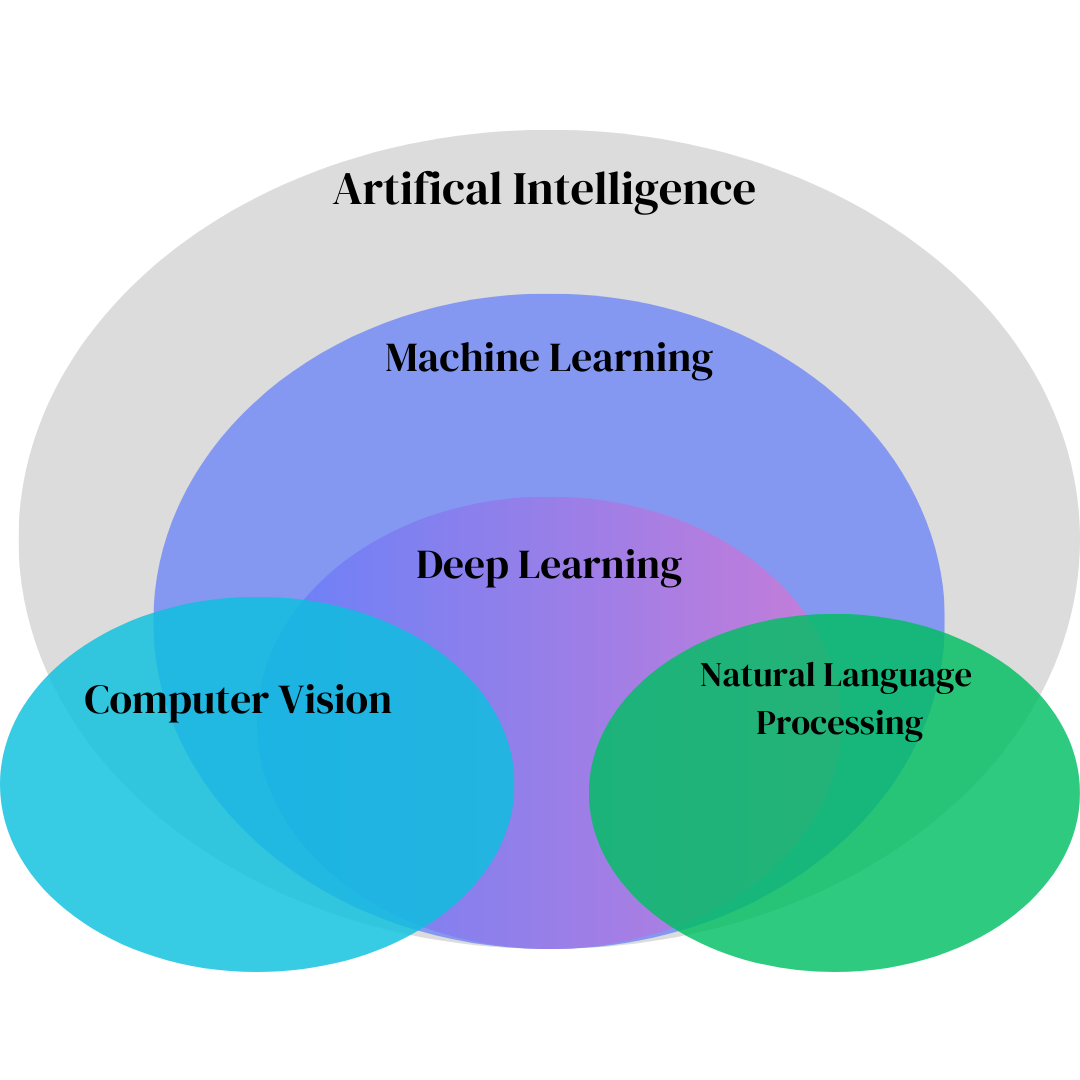
Overview of Computer Vision
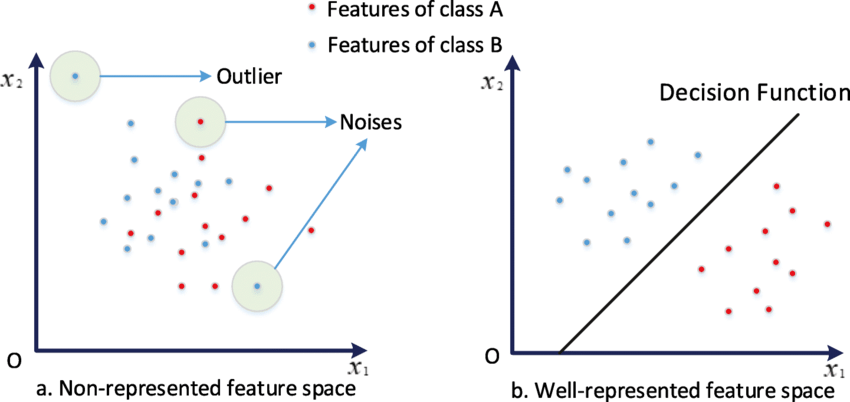
Core concepts in computer vision and machine learning
History of Computer Vision
How computer vision evolved through feature spaces
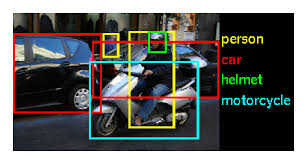
ImageNet Large Scale Visual Recognition Challenge
ImageNet's impact on modern computer vision
Region-CNNs
Traditional ML vs modern computer vision approaches
Distributed Systems
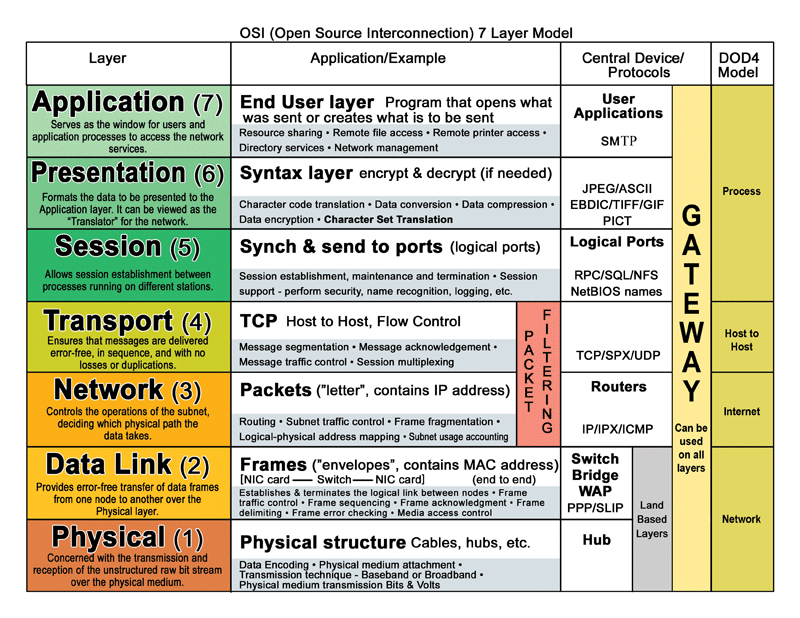
Overview of Distributed Systems
Fundamentals of distributed systems and the OSI model
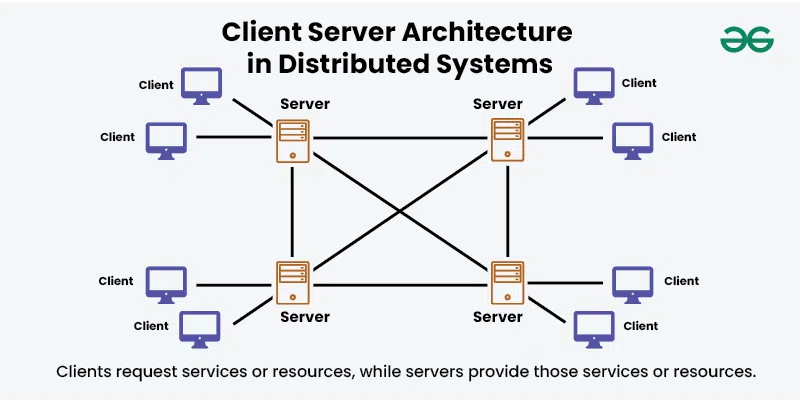
Distributed Systems Architectures
Common design patterns for distributed systems
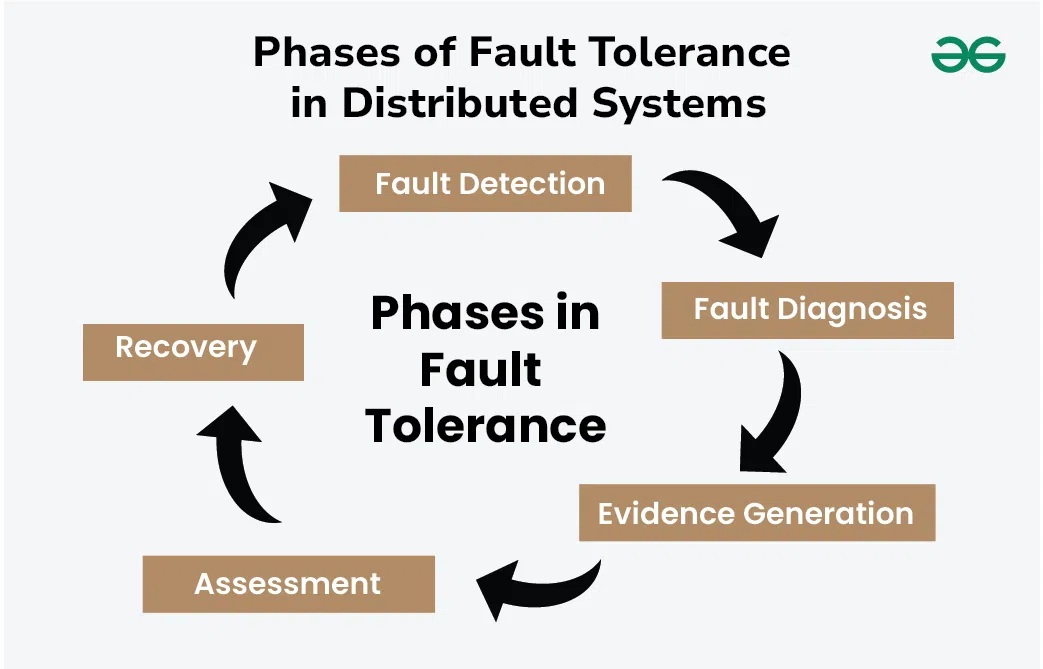
Dependability & Relevant Concepts
Reliability and fault tolerance in distributed systems
Marshalling
How data gets serialized for network communication
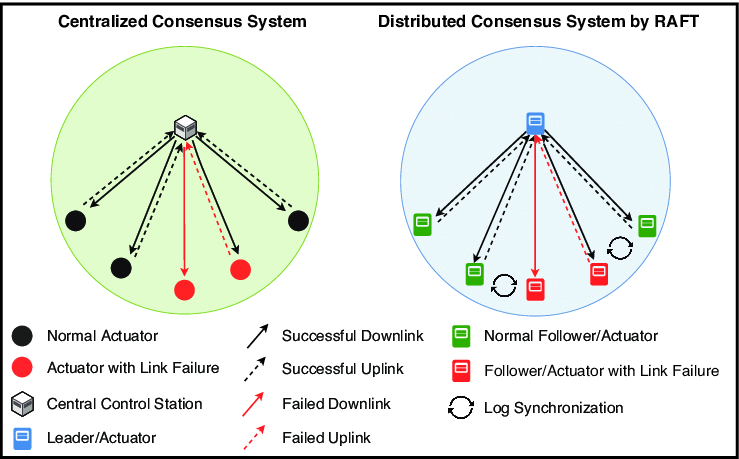
RAFT
Understanding the RAFT consensus algorithm
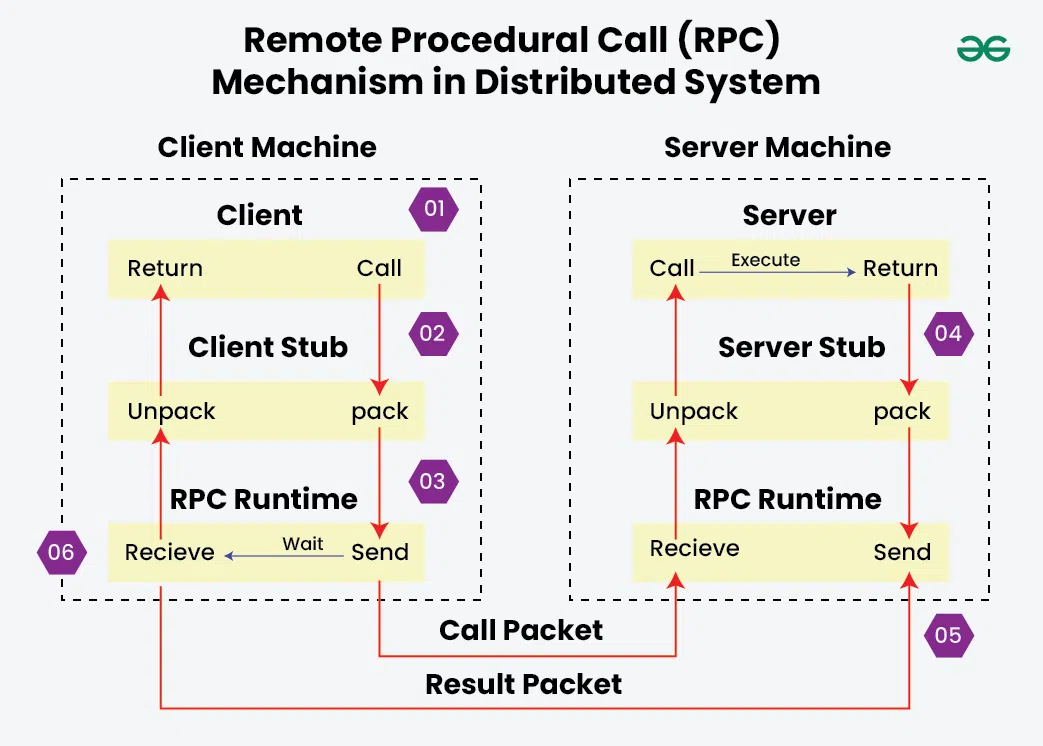
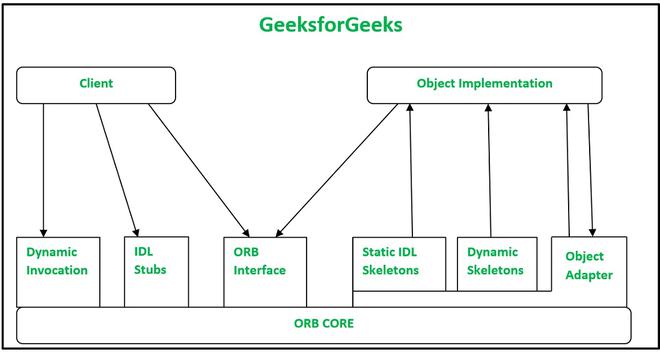
Remote Procedural Calls
How RPC enables communication between processes
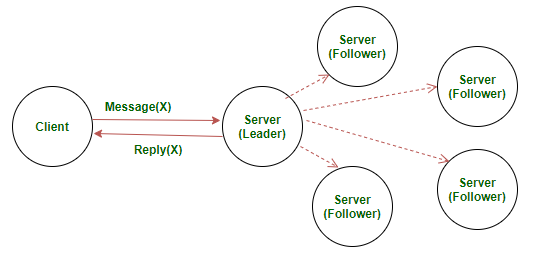
Servers
Server design and RAFT implementation
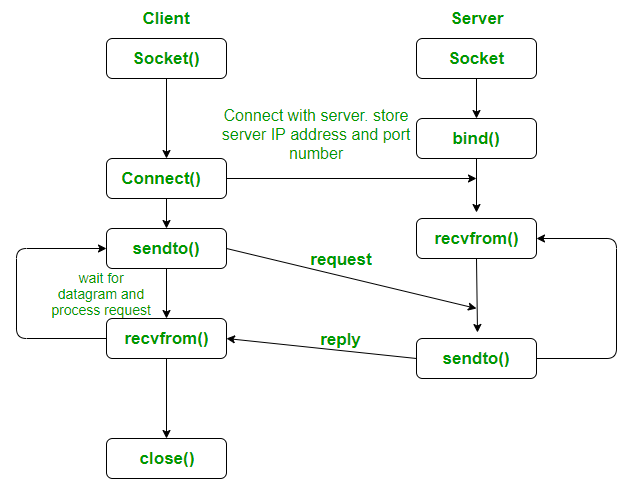
Sockets
Network programming with UDP sockets
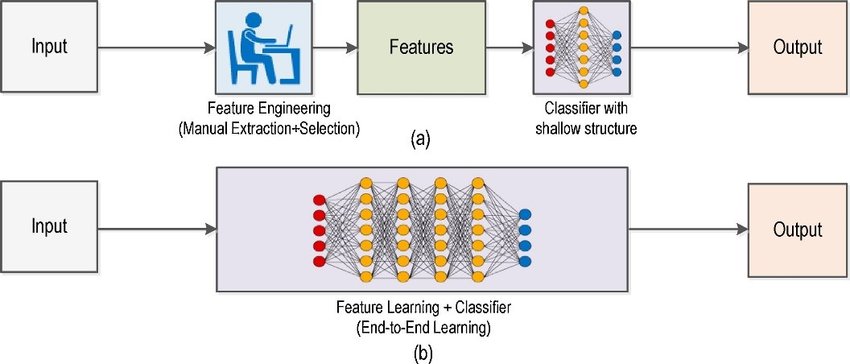
Machine Learning (Generally Neural Networks)
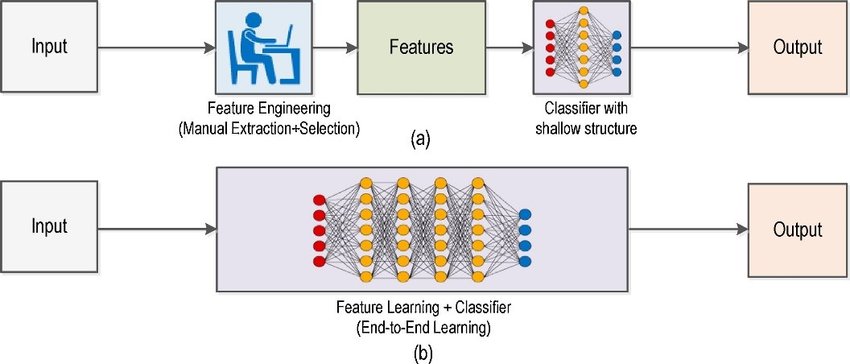
Anatomy of Neural Networks
Traditional ML vs modern computer vision approaches
LeNet Architecture
The LeNet neural network
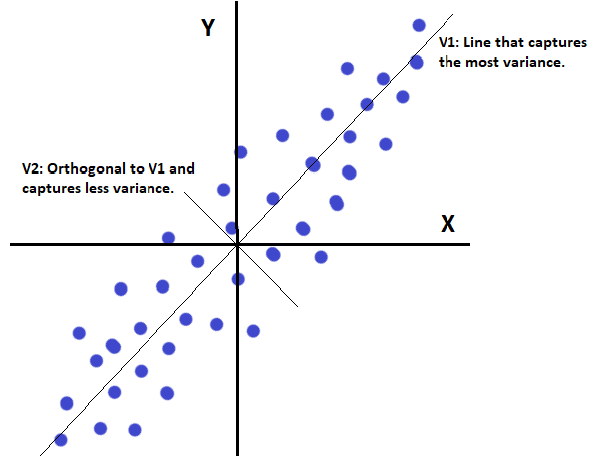
Principal Component Analysis
Explaining PCA from classical and ANN perspectives
Cryptography & Secure Digital Systems
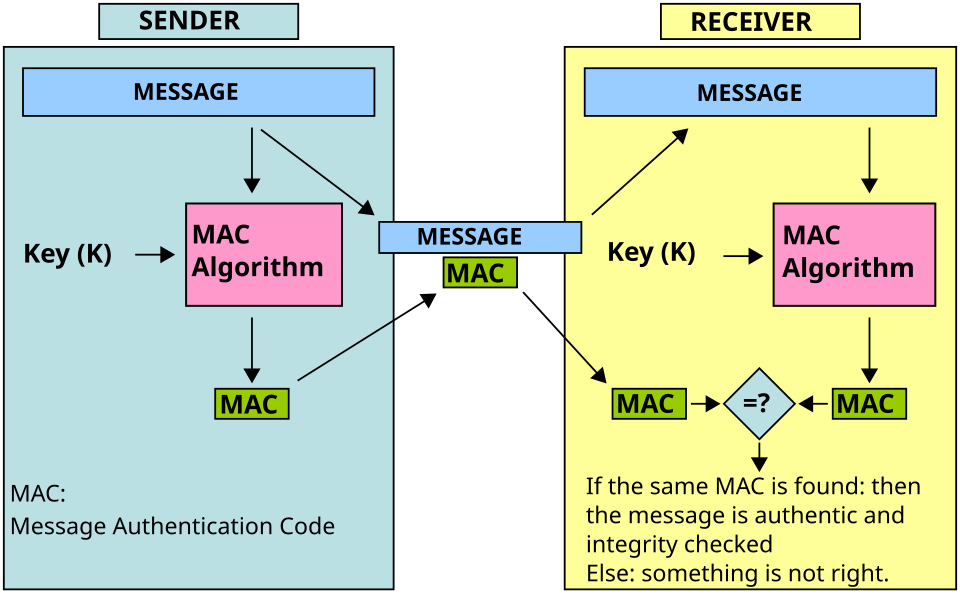
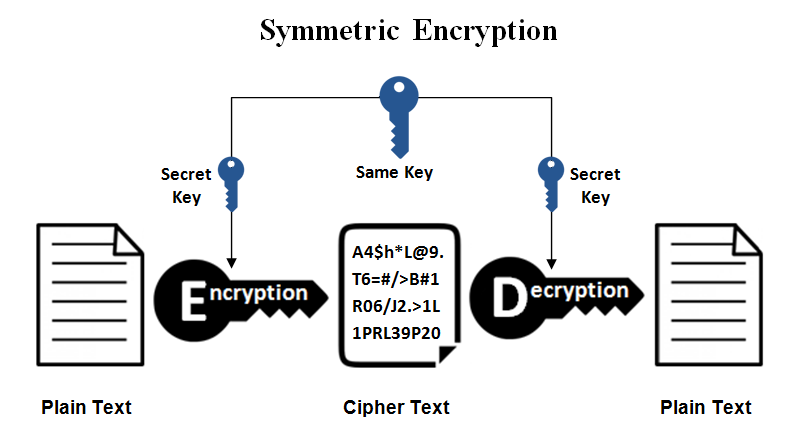
Symmetric Cryptography
covers MAC, secret key systems, and symmetric ciphers
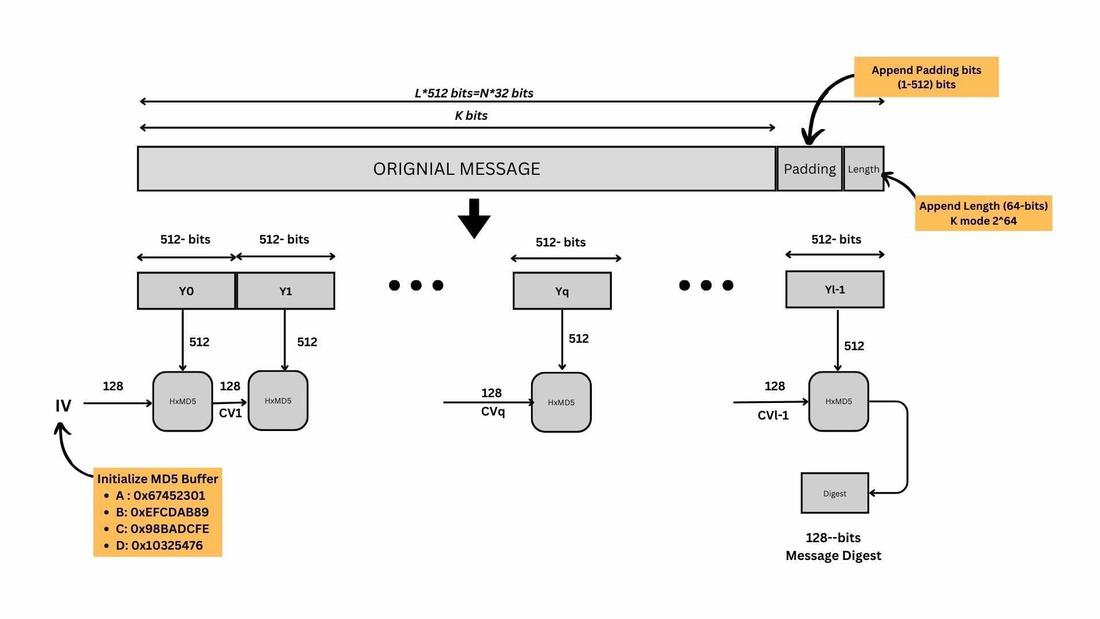
Hash Functions
Hash function uses in cryptographic schemes (no keys)
Public-Key Encryption
RSA, ECC, and ElGamal encryption schemes
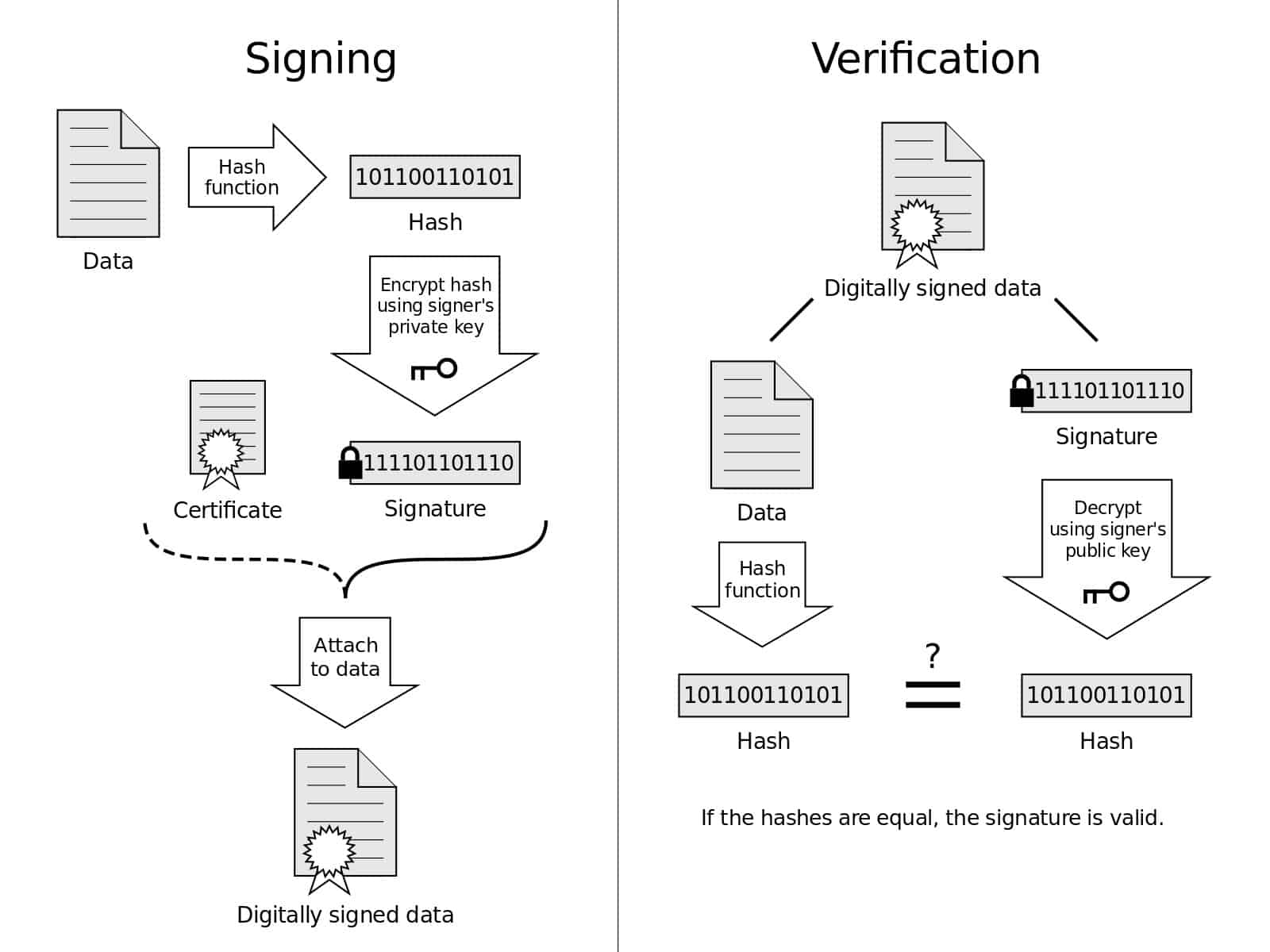
Digital Signatures & Authentication
Public-key authentication protocols, RSA signatures, and mutual authentication

Number Theory
Number theory in cypto - Euclidean algorithm, number factorization, modulo operations
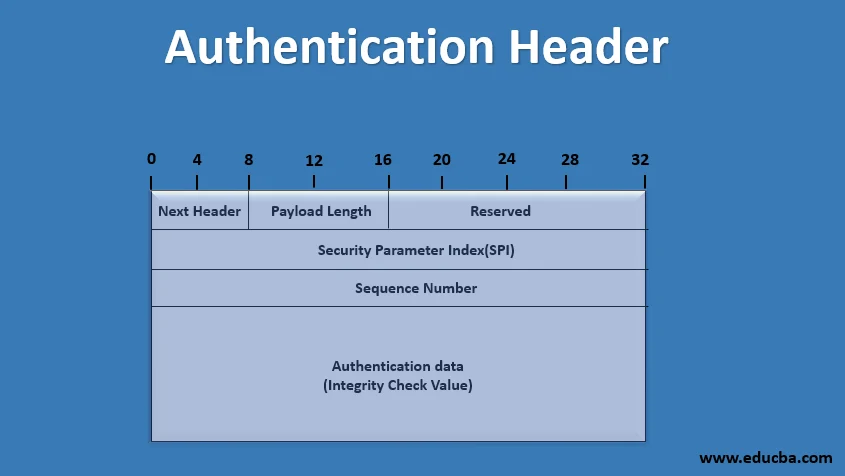
IPSec Types & Properties
Authentication Header (AH), ESP, Transport vs Tunnel modes